ArchiMate_SABSA
Practice of Modeling SABSA with the ArchiMate Specification

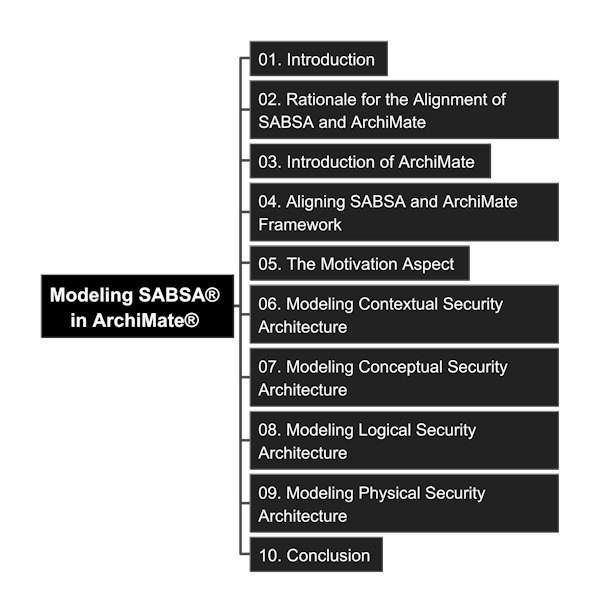
Read and Check Detail (Content in the Book)
- 01. Introduction
- 02. Rationale for the Alignment of SABSA® and ArchiMate®
- 03. An Introduction to the ArchiMate® Language
- 04. Aigning SABSA® and ArchiMate® Framework
- 05. The Motivation Aspect
- 06. Modeling Contextual Security Architecture
- 07. Modeling Conceptual Security Architecture
- 08. Modeling Logical Security Architecture
- 09. Modeling Physical Security Architecture
- 10. Conclusion
Resources
- This Guide “A Guide to Modeling SABSA® with the ArchiMate® Specification” can be downloaded from Open Group site: https://publications.opengroup.org/guides/archimate/g24b
- You may request variable SABSA® whitepaper from site: https://sabsa.org/white-paper-requests/, notice it would require you use your company’s business email address
Content Mindmap
Get Freeplane and click to open the MindMap (you need to Fork or Clone repository to your local to open it.)
You can check markdown format of mindmap if you haven’t installed Freeplane yet.
Brief Introduction
SABSA® (Sherwood Applied Business Security Architecture) is a methodology for developing risk-driven enterprise information security and information assurance architectures and for delivering security infrastructure solutions that support critical business initiatives. It is an open standard, comprising a number of frameworks, models, methods and processes, free for use by all, with no licensing required for end-user organizations who make use of the standard in developing and implementing architectures and solutions. (Source: W100 - SABSA® White Paper)
The Joint Working Group, between SABSA and the Open Group, was established around 2024, aims to following variable purpose:
- develop a settled consensus of core security elements, relationships, and properties - referred to collectively as the “Security Overlay”.
- propose a reference of vocabulary, patterns, and conventions in this domain, to further enterprise security as a practice, and encourage the wider appreciation of security concepts in general and the SABSA approach in particular.
- incentivize toolmakers to facilitate support for security within their products, no need to focus on how to model the security perspective.
The practice in this repository is to detail go through the guide, and using Archi (ArchiMate® modeling tool) to create the hands-on model step-by-step, so that it can be tailored by every architecture team to their own company’s EA+Security meta-model creation.
Extended Variable Views on SABSA
- SABSA Framework for Enterprise Architects (avolution)
- SABSA – In 3 Minutes, local copy: LINK
- Enterprise Security Architect - A Top-down Approach from ISACA in 2017, local copy: LINK
SABSA in comparison with other “Security” Framework
| SABSA | COBIT | NIST | |
|---|---|---|---|
| Primary Focus | Business-driven security architecture and risk-aligned design | Enterprise IT governance, performance, and compliance oversight | Cybersecurity risk management, and courity standards |
| Methodology | Layered architecture model driven by business risk context | Governance and management objectives, control frameworks, maturity models | Risk-based frameworks (CSF, RMF, SP8000 series) |
| Scope | End-to-end enterprise security architecture | Organization-wide IT governance and controls | Technical and operational cybersecurity |
| Purpose | Design security aligned with business risk | Ensure IT value and risk management | Establish effective security controls |
| Use Case | Zero-Trust architecture, identity design | IT governance audits, compliance | Cybersecurity implementation |
| Integration Insight | HOW security is architected | WHO governs and WHY controls matter | WHAT security controls to implement |
| Summary | Architecture Blueprint | HOW | Security Controls & Standards |
Thanks for sharing the great insight from Rechard Branson.
Other References
Tools Used for Demo and Tutorial
- Repository tracking: VS Code
- Video cover and contents: Microsoft Powerpoint or any slide tool
- Mindmap: FreePlane
- ArchiMate Modeling: Archi
- Schema Documentation in JSON: visualized via “JSON Crack” or “JSON Lens”, and many others similar extension
- Knowlege on Metamodel with relationship: Protégé
- Non-ArchiMate Diagramming, e.g. hierarchical chart: PlantUML
Modeling Tutorial Videos and Repositories
- YouTube Channel: YouTube Video List
- DouYin 抖音: Video List in DouYin
- Udemy Course: Modeling SABSA in ArchiMate using Archi (and Protege, PlantUML and JSON)
- Repository in Gitee: https://gitee.com/yasenstar/ArchiMate_SABSA
Markdown Editing Tips
Key in special character in Markdown through ALT + code (need to use number pad):
- « : Alt + 0171
- » : Alt + 0187
- ® : Copyright, Alt + 0174
- ™ : Alt + 0153
- é : Alt + 130
- ∞ : note that “Alt + 236 or 8734” is not working in my machine, instead, using Windows Emoji keyboard works (Press
Win + .then click `Symbols -> Math Symbols -> Select ∞)
Key in special characters in Markdown through HTML syntax:
- superscript: use “sup” tag
- subscript: use “sub” tag
Comments are welcome, leave your thoughts in Discussion Board. Last updated at 1/13/2026, 1:05:25 PM